CYBERSECURITY OT
From regulatory to operational compliance
Starting in 2027, compliance with OT Cybersecurity requirements will become mandatory for industrial companies.
Non-compliance can result in fines, operational impacts, and increased costs related to external specialist support.
Logbot supports companies on this journey by offering a three-phase Security Program that allows them to manage industrial cybersecurity in a structured, continuous, and autonomous manner, in line with relevant standards and regulations.
OUR SECURITY PROGRAM
We guide companies through a comprehensive industrial security journey, integrating tools, skills, and services.
Our Security Program follows a structured and progressive path: we begin with awareness, to understand security risks and standards; we continue with the introduction of best practices and the definition of an implementation plan;
we provide tools and procedures for concrete cybersecurity management, and we conclude with operational adoption, transforming training into real security integrated into daily processes.
Training
- Logbot training courses combine theory and practical workshops, customised and designed for:
- Develop a strong security culture within the company
- Increase awareness of industrial cyber risks
- Offer support from industrial cybersecurity experts throughout the process
Anlysis
- Functional analysis of customer systems:
- Gap analysis
- Security level
- Security design
- Report di validazione
- Audit completato
Tools
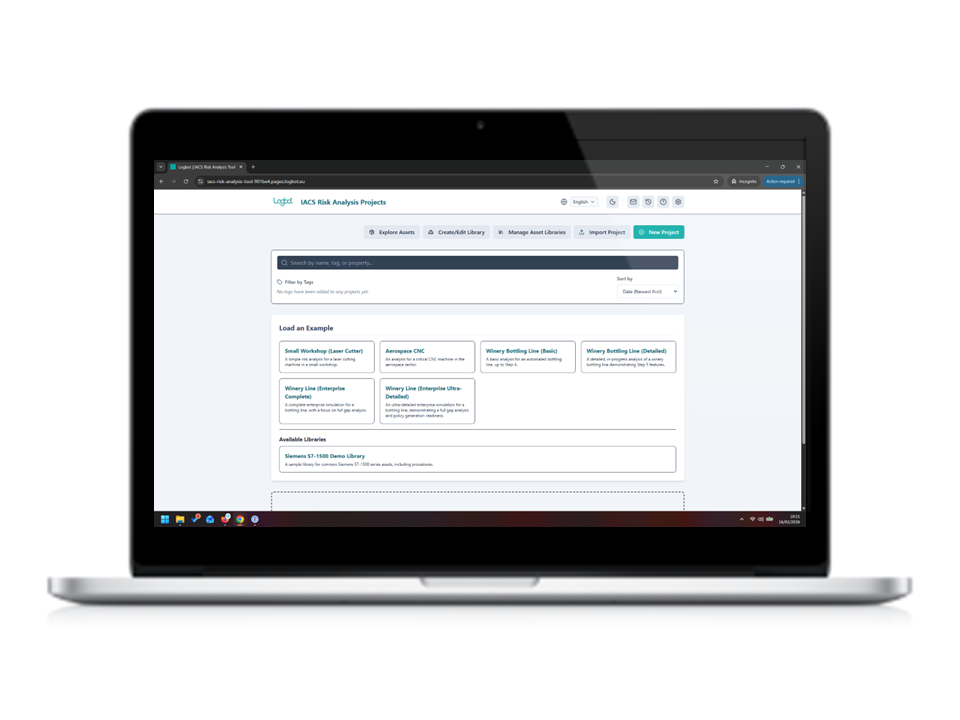
Delivery of the operational tool to independently manage security and compliance.
Logbot IACS Risk Analysis Tool (Logbot MACtool)
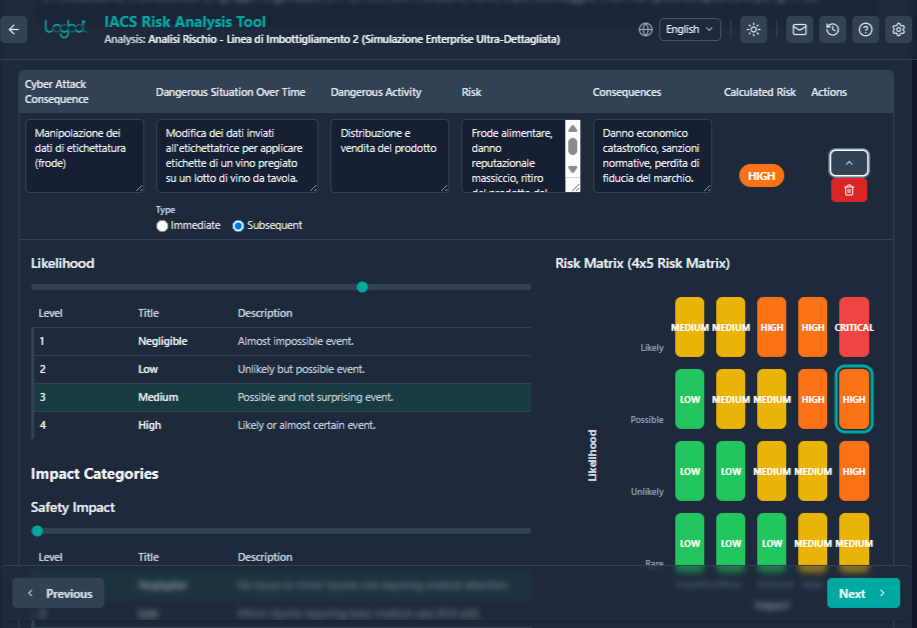
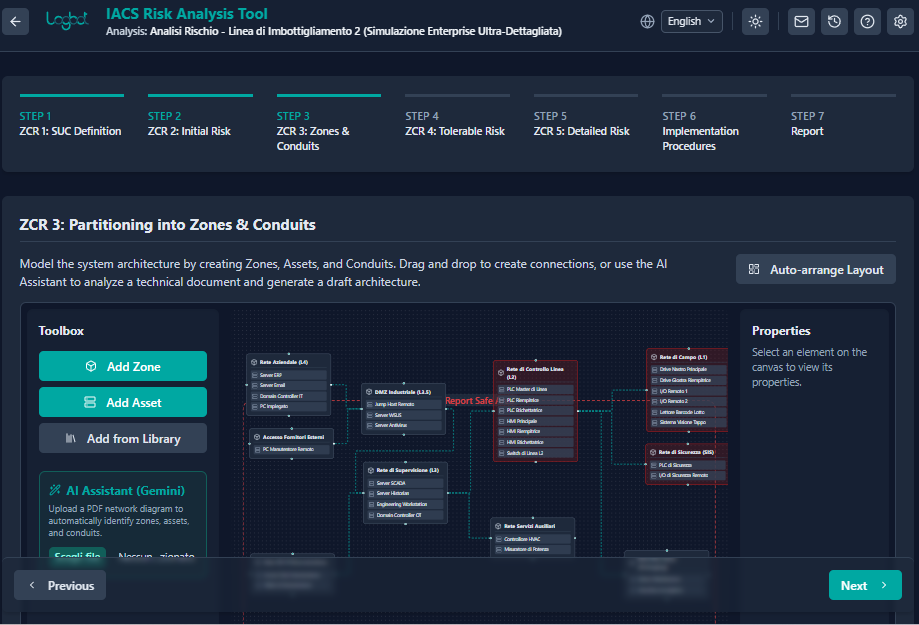
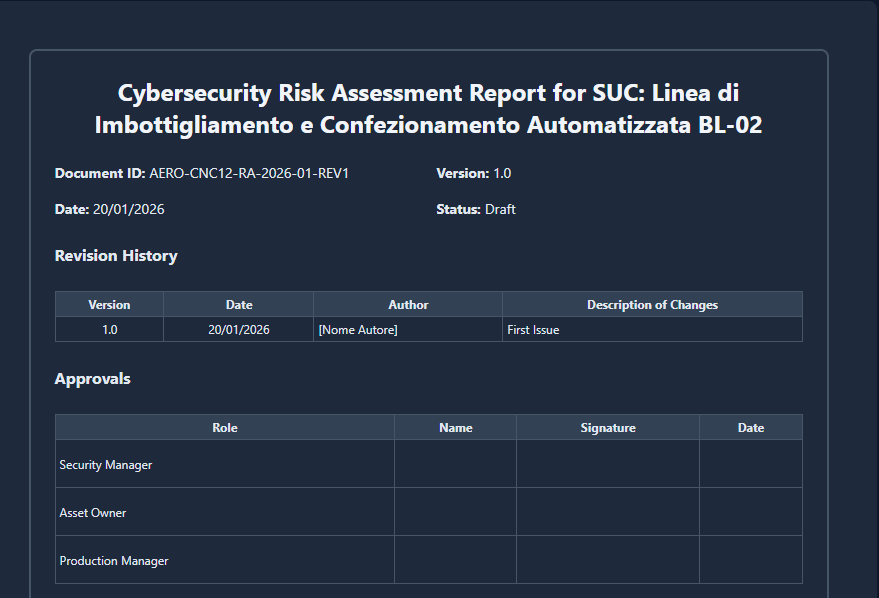
Logbot MACtool is a desktop software for machine manufacturers and system integrators that supports cybersecurity risk assessment according to IEC 62443-3-2, from the definition of the *SUC to the automatic generation of documentation, ensuring regulatory compliance in a rapid, structured way to CRA and the new machinery regulation.
Vantaggi di Logbot MACtool
| Category | Logbot MACtool | Others | |
| Audit speed | Complete automatic audit in a few hours | too long | |
| Cost | Fixed and low cost | High and variable | |
| Updates | Automatic and continuous | Slow and neglected | |
| Scalability | Unlimited, more machines and lines | Limited | |
| Traceability & documentation | Automatically generated audit trails, versioning, and policies | Manual with risk of errors | |
| Regulatory support | IEC 62443 natively encoded | Depends on the consultant |
LOGBOT MACTool SOFTWARE LICENSE
|
|
|
|
|
|
|---|---|---|---|---|
|
|
Code | Package name | Description | Projects included |
|
|
SWA-RA-SUB-005 | Entry Level | Ideal for small OEMs or independent consultants. Includes all basic features and standard reporting with email support. |
5 |
|
|
SW-RA-SUB-020 | Professional | The standard choice for structured OEMs. Includes advanced AI capabilities, asset library management, and priority support. | 20 |
|
|
SW-RA-SUB-050 | Enterprise | For large system integrators and OEMs. Large-scale projects, report customization, and training sessions. | 50 |
FAQ
What is the MACTool?
What activities does it specifically cover?
What regulations does it help meet?
MACTool directly covers the work required for IEC 62443-3-2 and IEC 62443-3-3, i.e., the machine/plant/IACS system level: zoning and conduits, risk assessment, security level definition and justification, gap analysis, and remediation.
For CRA and the New Machinery Regulation, MACTool is very useful because it produces and organizes the technical evidence, risk structure, and documentation needed to support the machine's compliance process.
For NIST, MACTool is an excellent operational foundation for Identify, Protect, and risk management activities, thanks to the management of assets, perimeter, scenarios, gaps, and mitigations.
How does risk assessment work with MACTool?
How are Security Levels defined?
What outputs does it produce?
Where does the data reside?
Is the data still portable?
Does the customer retain control of the data?
Is it suitable for multiple machines or product families?
Is initial training provided?
Contact us
PROTECT AND AUTOMATE YOUR SYSTEMS